IT Security Tips
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Latest Blog Post
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Cybersecurity Awareness Month – Week 3: Why You Should Consider a Cyber Career
Cybersecurity is one of the hottest sectors today, with new threats and challenges emerging each day. And with that, there is a huge push being undertaken by both business and education sectors to attract individuals toward a degree and career in...
Cybersecurity Awareness Month – Week 2: 3 Fundamentals for Shoring Up Phishing Defenses
From ransomware to cyber attacks, the cybersecurity space has been as hectic as it has ever been over the last 12-24 months. However, for all of the emerging threats and news that are cropping up on the horizon, phishing -- one of the oldest pain...
Cybersecurity Awareness Month – Week 1: Get Familiar with the Cyber Basics
At a time when we are more connected than ever, being “cyber smart” is of the utmost importance. This year has already seen more than a fair share of attacks and breaches, including the SolarWinds and Kaseya breaches as well as high-profile attacks...
Trending: Coronavirus Phishing Scams and Fake Websites
Recently, there has been a new trending topic in the cybersecurity industry. Coronavirus. Cybercriminals are preying on the fears of individuals around the world as coverage of the coronavirus pandemic increases again. Scammers are exploiting the...
IT Security Tips

5 Mistakes to Avoid in Business Continuity Planning
Your Business Continuity Plans may look great on paper, but they aren’t worth a thing if you don’t have buy-in from...

Cyber Insurance FAQ’s
A cyber risk refers to the risk of financial harm that is done to an organization and is a result of a failure or...

What to do if important emails are landing in your junk folder
At some point in your career you’ve missed an email you should have received. Perhaps it was an RFP you were waiting...

8 Reasons to Purchase Cyber Insurance
Cyber insurance is an important way to protect you and your business from cyberattacks that happen regularly across...

5 Compelling Reasons to Upgrade to Microsoft 365 Business Premium
What is Microsoft 365 Business Premium? Microsoft 365 is the productivity cloud that brings together best-in-class...

Staying online efficient in 2021
2020 was a tough year for many businesses, and 2021 has its own share of challenges too. “We’ve had a lot of companies...

Why every company needs Cyber Insurance
A Quick Overview of Cyber Insurance Nearly every company, of every size, is exposed and vulnerable to cyberattacks....

Audio maker Bose reveals data breach after ransomware attack
Bose reveals it suffered “a sophisticated cyber-attack that disrupted some of its systems” in the United States....
Lie, lie, lie!
Social engineering is big business. What is it? Figuring out who you are and then using that information to make money...
Are you backing up your WEBSITE?
While most businesses understand the importance of backing up their server and files, many forget to back up their...
Keep sensitive and important data off DEVICES and in the cloud
If a laptop is stolen or lost, and the data is not backed up, you just lost it all. Worst of all, even if you had it...

7 useful tools for a quick and easy digital spring cleaning
After a year mostly spent at home channeling Marie Kondo, I bet you're like me, and every drawer, closet, and room is...
How even a STRONG password can work against you
There are two mistakes we see with usernames and passwords, even if they are GOOD strong ones. The first is using the...

Breach Victims File Class Action Lawsuit Against Einstein Healthcare
In January 2021, Einstein Healthcare began its public notifications for a weeks-long email hack that occurred nearly...

New Apple iOS update bolsters user privacy
JOPLIN, Mo. — If you don’t like the idea of tech companies tracking where you go and what you do online, a new...
Why you might want to cover up your webcam with a sticker
Here’s a disturbing, but very real, tactic for hackers: spying on you via your device’s camera. Some simply watch you...

How to protect your technology before a disaster
Photos, bank statements, and tax records are just a few of the things at risk if you don’t safeguard your technology...
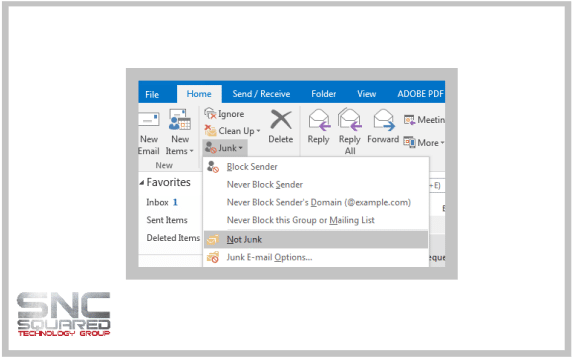
Missing Emails in Outlook? Check your junk folder.
Sometimes, seemingly for no apparent reason, Outlook or Outlook Web App (OWA) will put genuine email into your Junk...

Self-Assessment: How strong is Your Cybersecurity Plan?
Anyone who has a small to medium-sized business has “an” IT plan, but per a recent study, only 14% of them rate their...

Disaster Readiness and Recovery
As we come upon another Tornado Season, we want to take a moment to remind our fellow Four-States area...

6 Ways Financial Institutions Can Improve Their Cybersecurity Strategy
With the delicate nature of the data handled by financial institutions, it’s no wonder that this industry remains one...

Network Doctor earns top rankings as MSP and solution provider
We’re excited to announce that we’ve been recognized once again for our success within the Healthcare vertical as one...

What is an MSP (Managed Service Provider)?
Many of us have heard the term “managed services provider,” but exactly what is an MSP, anyway? An MSP is a company...
Don’t download ANYTHING you’re not authorized to download
So you have a big file you need to get over to your printer YESTERDAY and you can’t get it to “send” via e-mail...

Bank online? Do this ONE thing…
If you do online banking, NEVER access your online account with a PC or device that you use to log in to social media...

Is Microsoft Business 365 right for your business?
Is Microsoft Business 365 right for your business? Microsoft Business and Enterprise editions offer a suite of online...

The Importance of a PC Refresh Cycle
Over the past 2 years, I have been investing more time and money in my newfound love/hate relationship with running....
My IT Guy Quit, Now What?
Receiving a resignation letter from your IT manager can set off the panic alarm – and for good reason. Most...

CRN Names NETWORK DOCTOR To Its 2021 MSP 500 List
CRN®, a brand of The Channel Company, has named Network Doctor to its 2021 Managed Service Provider (MSP) 500...

What Business Executives Want to Know About Cyber Risk
Who should you call first after you’ve had a data breach? What should be included in a cyber attack...

Pros and Cons between Cloud and On-Premise Solutions
What is better: on-premises or cloud? Many established companies wonder if it’s worth it to transition out of their...

This can happen at work OR at your home
In a recent incident reported in US news, an office secretary unknowingly gave some of her law firm’s most private...

8 Reasons SMBs are a Top Target For Cyber Attacks
Savvy hackers can easily disrupt your system, stealing sensitive data and even comprising your finances. They can also...

Hybrid Cloud Computing – How It Works?
A hybrid cloud computing environment uses a mix of on-premise, private cloud and third-party, public cloud services...

5 Things A World-Class Managed Service Provider Must Have
More and more small and midsize businesses are turning to managed service providers to manage and maintain their...

If you’ve ever said this, you’re ASKING to be hacked!
Want to know what every hacker hopes you believe? “We’re small…nobody wants to hack us.” This is the #1 reason why...

The complete guide to start using Microsoft Teams in 2021
Quick links to teams topics Microsoft Teams Basics Posts Pane — Pin Messages in Teams Wiki in...

The #1 threat to your security is…
YOU! And your employees. Like it or not, human beings are our own worst enemies online, inviting hackers, viruses,...

7 Services You Should Receive From Your Managed Services Provider
Comparing managed service providers (MSPs) isn’t always easy—especially if IT isn’t your forte. Without an advanced...

10 Best Microsoft Teams Integrations You Need To Try
Microsoft Teams is a platform that brings together all of your workplace tools, apps, and services to deliver...

Fighting cybercrime: FBI says over $4.2 billion lost in 2020
The intention of this article is not just to put scary numbers out there. We have enough FUD (fear, uncertainty, and...
Three essential rules for all cloud applications
If you’re using any kind of cloud application (and these days, who isn’t?), you are right to be concerned about data...
Cybersecurity
Cybersecurity is an umbrella term that covers all of the technologies and processes used to keep computer systems and...

The Dangers of Public WiFi
Have you ever used Starbucks WiFi? Ever been to a conference, airport, or hotel and used their public...

How Can Your Company Improve Technology without Overspending?
For small or medium-sized businesses, a lean budget and increased cost efficiency are the keys to a healthy bottom...

Top 5 Technology Trends Moving Into 2021
To retool for the world of tomorrow, companies should stay on top of these critical digital trends. Necessity being...

You’ve been HACKED! What’s the first thing you should do?
No matter how diligent you are about security, there’s always a chance you can get hacked. That’s why you need to put...

Network Doctor Featured at Automation Nation 2018
There was a time when we did some systems integration, found a solution for a partner, handled a one-time...

March 2021 – Women’s History Month – Women in Tech
March is the special time of year where the immeasurable impact women have made on society is commemorated. From the...
A WARNING if you handle, process or store client credit cards
If you handle, process or store credit cards in any manner, you are required to comply with PCI DSS, or Payment Card...

Apple users targeted by ‘mysterious’ malware
The "unusual" Silver Sparrow strain silently affected systems in more than 150 countries around the world. It was...

Your firewall is USELESS unless…
A firewall is a device that acts like a security cop watching over your computer network to detect unauthorized access...
Why do companies hesitate when it comes to Outsourcing IT?
People are often scared of what they do not know. This is true with technology as well. With the internet at our...
As Seen On TV
Benefits of recycling electronics
The holidays are a popular time to upgrade devices like cell phones, laptops, and tablets, leading to old devices gathering dust. John Motazedi, SNC Squared, said, “Everyone gets new electronics, you get new games, new technology, phones. Computers, tablets.” And just...